在HTTP中,HTTP基本认证(Basic Authentication)是一种允许网页浏览器或其他客户端程序以(用户名:口令) 请求资源的身份验证方式,不要求cookie,session identifier、login page等标记或载体。
- 所有浏览器据支持HTTP基本认证方式
- 基本身证原理不保证传输凭证的安全性,仅被based64编码,并没有encrypted或者hashed,一般部署在客户端和服务端互信的网络,在公网中应用BA认证通常与https结合
https://en.wikipedia.org/wiki/Basic_access_authentication
BA标准协议
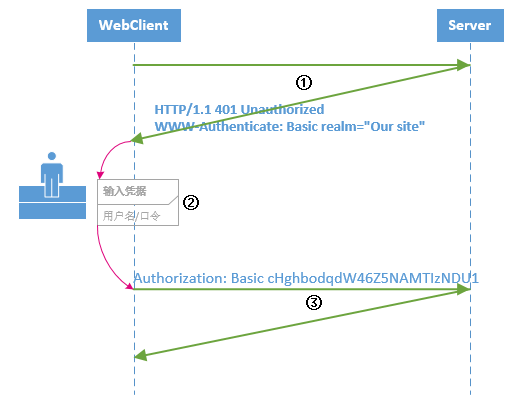
BA认证协议的实施主要依靠约定的请求头/响应头,典型的浏览器和服务器的BA认证流程:
① 浏览器请求应用了BA协议的网站,服务端响应一个401认证失败响应码,并写入WWW-Authenticate响应头,指示服务端支持BA协议
HTTP/1.1 401 Unauthorized
WWW-Authenticate: Basic realm="our site" # WWW-Authenticate响应头包含一个realm域属性,指明HTTP基本认证的是这个资源集
或客户端在第一次请求时发送正确Authorization标头,从而避免被质询
② 客户端based64(用户名:口令),作为Authorization标头值 重新发送请求。
Authorization: Basic userid:password
所以在HTTP基本认证中认证范围与 realm有关(具体由服务端定义)
> 一般浏览器客户端对于www-Authenticate质询结果,会弹出口令输入窗.
BA编程实践
aspnetcore网站利用FileServerMiddleware 将路径映射到某文件资源, 现对该 文件资源访问路径应用 Http BA协议。
ASP.NET Core服务端实现BA认证:
① 实现服务端基本认证的认证过程、质询逻辑
②实现基本身份认证交互中间件BasicAuthenticationMiddleware ,要求对HttpContext使用 BA.Scheme
③ASP.NET Core 添加认证计划 , 为文件资源访问路径启用 BA中间件,注意使用UseWhen插入中间件
using System; using System.Net.Http.Headers; using System.Security.Claims; using System.Text; using System.Text.Encodings.Web; using System.Threading.Tasks; using Microsoft.AspNetCore.Authentication; using Microsoft.Extensions.Logging; using Microsoft.Extensions.Options; namespace EqidManager.Services { public static class BasicAuthenticationScheme { public const string DefaultScheme = "Basic"; } public class BasicAuthenticationOption:AuthenticationSchemeOptions { public string Realm { get; set; } public string UserName { get; set; } public string UserPwd { get; set; } } public class BasicAuthenticationHandler : AuthenticationHandler<BasicAuthenticationOption> { private readonly BasicAuthenticationOption authOptions; public BasicAuthenticationHandler( IOptionsMonitor<BasicAuthenticationOption> options, ILoggerFactory logger, UrlEncoder encoder, ISystemClock clock) : base(options, logger, encoder, clock) { authOptions = options.CurrentValue; } /// <summary> /// 认证 /// </summary> /// <returns></returns> protected override async Task<AuthenticateResult> HandleAuthenticateAsync() { if (!Request.Headers.ContainsKey("Authorization")) return AuthenticateResult.Fail("Missing Authorization Header"); string username, password; try { var authHeader = AuthenticationHeaderValue.Parse(Request.Headers["Authorization"]); var credentialBytes = Convert.FromBase64String(authHeader.Parameter); var credentials = Encoding.UTF8.GetString(credentialBytes).Split(':'); username = credentials[0]; password = credentials[1]; var isValidUser= IsAuthorized(username,password); if(isValidUser== false) { return AuthenticateResult.Fail("Invalid username or password"); } } catch { return AuthenticateResult.Fail("Invalid Authorization Header"); } var claims = new[] { new Claim(ClaimTypes.NameIdentifier,username), new Claim(ClaimTypes.Name,username), }; var identity = new ClaimsIdentity(claims, Scheme.Name); var principal = new ClaimsPrincipal(identity); var ticket = new AuthenticationTicket(principal, Scheme.Name); return await Task.FromResult(AuthenticateResult.Success(ticket)); } /// <summary> /// 质询 /// </summary> /// <param></param> /// <returns></returns> protected override async Task HandleChallengeAsync(AuthenticationProperties properties) { Response.Headers["WWW-Authenticate"] = $"Basic realm=\"{Options.Realm}\""; await base.HandleChallengeAsync(properties); } /// <summary> /// 认证失败 /// </summary> /// <param></param> /// <returns></returns> protected override async Task HandleForbiddenAsync(AuthenticationProperties properties) { await base.HandleForbiddenAsync(properties); } private bool IsAuthorized(string username, string password) { return username.Equals(authOptions.UserName, StringComparison.InvariantCultureIgnoreCase) && password.Equals(authOptions.UserPwd); } } }
