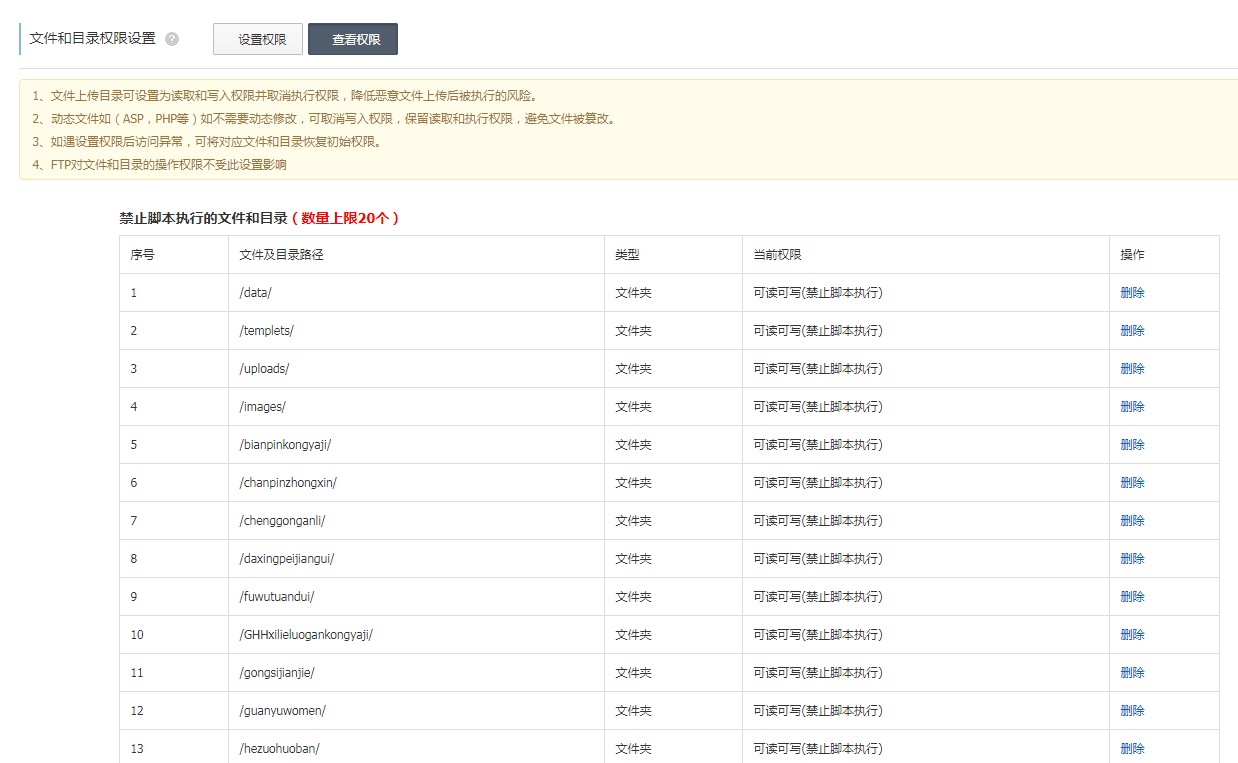
①有条件的用户把中 data、templets、uploads、a(可删)、special(可删)、images、install(装后删)目次配置为不答允执行剧本,include、plus、dede目次克制写入,系统将更安详;
②权限配置一般通过主机节制面板,好比阿里云的文件和目次权限配置、西部数码的文件掩护等等。
③老版本若登录靠山提示验证码错误,选中/data目次,将权限配置为完全节制(可读可写)权限
(此图片来历于网络,如有侵权,请接洽删除! )
安详配置四:主机安详防护主机安详防护只针对独立处事器可能VPS。
WIN处事器:可以安装安详狗、『D盾_防火墙』
LINUX处事器:网站防篡改措施、宝塔系统加固;
②、裂痕文件 /dede/media_add.php
这是靠山文件任意上传裂痕(上面有说删除此文件,假如不删除,需要利用这个成果,那么修改以下代码补掉裂痕)
$fullfilename = $cfg_basedir.$filename; 修改为 if (preg_match('#.(php|pl|cgi|asp|aspx|jsp|php5|php4|php3|shtm|shtml)[^a-zA-Z0-9]+$#i', trim($filename))) { ShowMsg("你指定的文件名被系统克制!",'javascript:;'); exit(); } $fullfilename = $cfg_basedir.$filename;③、裂痕文件 /include/uploadsafe.inc.php (修改两个处所) $image_dd = @getimagesize($$_key); 修改为 $image_dd = @getimagesize($$_key); if($image_dd == false){ continue; }
${$_key.'_size'} = @filesize($$_key);} 修改为 ${$_key.'_size'} = @filesize($$_key);} $imtypes = array("image/pjpeg", "image/jpeg", "image/gif", "image/png", "image/xpng", "image/wbmp", "image/bmp"); if(in_array(strtolower(trim(${$_key.'_type'})), $imtypes)) { $image_dd = @getimagesize($$_key); if($image_dd == false){ continue; } if (!is_array($image_dd)) { exit('Upload filetype not allow !');} }
安详配置六、SQL注入裂痕 ①、裂痕文件 /include/filter.inc.php (或许在46行)
return $svar;
修改为
return addslashes($svar);
②、裂痕文件 /plus/search.php (或许在109行)
$keyword = addslashes(cn_substr($keyword,30));
修改为
$typeid = intval($typeid); $keyword = addslashes(cn_substr($keyword,30));
③、裂痕文件 /member/mtypes.php (或许在71行)
$query = "UPDATE `dede_mtypes` SET mtypename='$name' WHERE mtypeid='$id' AND mid='$cfg_ml->M_ID'";
修改为
$id = intval($id); $query = "UPDATE `dede_mtypes` SET mtypename='$name' WHERE mtypeid='$id' AND mid='$cfg_ml->M_ID'";
⑤、裂痕文件 /plus/guestbook/edit.inc.php (或许在55行) $dsql->ExecuteNoneQuery("UPDATE `dede_guestbook` SET `msg`='$msg', `posttime`='".time()."' WHERE id='$id' "); 修改为 $msg = addslashes($msg); $dsql->ExecuteNoneQuery("UPDATE `dede_guestbook` SET `msg`='$msg', `posttime`='".time()."' WHERE id='$id' ");;
⑥、裂痕文件 /member/soft_add.php (或许在154行) $urls .= "{dede:link islocal='1' text='{$servermsg1}'} $softurl1 {/dede:link} "; 修改为 if (preg_match("#}(.*?){/dede:link}{dede:#sim", $servermsg1) != 1) { $urls .= "{dede:link islocal='1' text='{$servermsg1}'} $softurl1 {/dede:link} "; }
⑦、裂痕文件 /member/article_add.php (或许在83行,cookies泄漏导致SQL裂痕) if (empty($dede_fieldshash) || $dede_fieldshash != md5($dede_addonfields.$cfg_cookie_encode)) 修改为 if (empty($dede_fieldshash) || ( $dede_fieldshash != md5($dede_addonfields . $cfg_cookie_encode) && $dede_fieldshash != md5($dede_addonfields . 'anythingelse' . $cfg_cookie_encode)))
⑧、裂痕文件 /member/album_add.php (约莫220行,对输入参数mtypesid未举办int整型转义,导致SQL注入产生) $description = HtmlReplace($description, -1);//2011.06.30 增加html过滤 (by:织梦的鱼) 修改为 $description = HtmlReplace($description, -1);//2011.06.30 增加html过滤 (by:织梦的鱼) $mtypesid = intval($mtypesid);
⑨、裂痕文件 /member/inc/inc_archives_functions.php (或许在239行,cookies泄漏导致SQL裂痕) echo "<input type="hidden" name="dede_fieldshash" value="".md5($dede_addonfields.$cfg_cookie_encode)."" />"; 修改为 echo "<input type="hidden" name="dede_fieldshash" value="". md5($dede_addonfields . 'anythingelse' .$cfg_cookie_encode) ."" />";
⑩、裂痕文件 /include/common.inc.php (SESSION变量包围导致SQL注入裂痕,最新的版本中已经修复) if( strlen($svar)>0 && preg_match('#^(cfg_|GLOBALS|_GET|_POST|_COOKIE)#',$svar) ) 修改为 if( strlen($svar)>0 && preg_match('#^(cfg_|GLOBALS|_GET|_POST|_COOKIE|_SESSION)#',$svar) )
⑪、裂痕文件 /include/payment/alipay.php (付出模块注入裂痕,此裂痕织梦官方在最新的版本中已经修复) $order_sn = trim($_GET['out_trade_no']); 修改为 $order_sn = trim(addslashes($_GET['out_trade_no']));
⑫、裂痕文件 /include/dedesql.class.php (或许在590行) if(isset($GLOBALS['arrs1'])) 修改为 $arrs1 = array(); $arrs2 = array(); if(isset($GLOBALS['arrs1']))
⑬、裂痕文件 /member/inc/archives_check_edit.php (或许第92行,dedecms前台任意文件删除(需要会员中心),颁发文章处,对付编辑文章的时候图片参数处理惩罚不妥,导致了任意文件删除) $litpic =$oldlitpic; 修改为 $litpic =$oldlitpic; if (strpos( $litpic, '..') !== false || strpos( $litpic, $cfg_user_dir."/{$userid}/" ) === false) exit('not allowed path!');
安详配置五:无用文件中的风险代码删除 ① dede empletslogin_ad.htm(这是织梦默认靠山登岸界面的告白代码,没用,删除以下这段代码) <!--<script type="text/javascript" src=http://www.dede58.com/"<?php echo UPDATEHOST;?>/dedecms/loginad.<?php echo $cfg_soft_lang; ?>.js"></script>--> <div class="dede-ad"> <ul> <script type="text/javascript"src="?action=single&key=admcploginad&charset=gbk"></script> </ul> </div>
② dede empletsindex_body.htm(织梦的靠山首页模板文件,删除以下这段告白代码) <iframe name="showad" src=http://www.dede58.com/"index_body.php?dopost=showad" frameborder="0" width="100%" id="showad" frameborder="0" scrolling="no" marginheight="5"></iframe>
③ dedemodule_main.php(向织梦官网发送卸载或安装插件的信息,若处事器设置不高,或不支持收罗(下载),那会卡死!注释掉以下代码) SendData($hash);//321行 SendData($hash,2);//527行
④ include aglib link.lib.php(织梦官方友链上传的代码,没有用,删除,不然占用机能,甚至卡死) else if($typeid == 999) { } //将{}里的以及上面的else全部删除
⑤ includededemodule.class.php(版本检测代码,30分钟一次,要扫描文件的!为什么打点模块打不开的原因就在这里,网站设置低的,卡死!) if(file_exists($cachefile) && (filemtime($cachefile) + 60 * 30) > time()) 修改为 if(file_exists($cachefile) && filesize($cachefile) > 10)
⑥ includededesql.class.php(下面这段代码会给网站加友情链接及版权"Power by DedeCms",删除) $arrs1 = array(0x63,0x66,0x67,0x5f,0x70,0x6f,0x77,0x65,0x72,0x62,0x79); $arrs2 = array(0x20,0x3c,0x61,0x20,0x68,0x72,0x65,0x66,0x3d,0x68,0x74,0x74,0x70,0x3a,0x2f,0x2f,0x77,0x77,0x77,0x2e,0x64,0x65,0x64,0x65,0x63,0x6d,0x73,0x2e,0x63,0x6f,0x6d,0x20,0x74,0x61,0x72,0x67,0x65,0x74,0x3d,0x27,0x5f,0x62,0x6c,0x61,0x6e,0x6b,0x27,0x3e,0x50,0x6f,0x77,0x65,0x72,0x20,0x62,0x79,0x20,0x44,0x65,0x64,0x65,0x43,0x6d,0x73,0x3c,0x2f,0x61,0x3e); //非凡操纵 $arrs1 = array(); $arrs2 = array(); if(isset($GLOBALS['arrs1'])) { $v1 = $v2 = ''; for($i=0;isset($arrs1[$i]);$i++) { $v1 .= chr($arrs1[$i]); } for($i=0;isset($arrs2[$i]);$i++) { $v2 .= chr($arrs2[$i]); } $GLOBALS[$v1] .= $v2; }
⑦ includecommon.func.php(会给网站加版权的,删除) $arrs1 = array(0x63,0x66,0x67,0x5f,0x70,0x6f,0x77,0x65,0x72,0x62,0x79); $arrs2 = array(0x20,0x3c,0x61,0x20,0x68,0x72,0x65,0x66,0x3d,0x68,0x74,0x74,0x70,0x3a,0x2f,0x2f, 0x77,0x77,0x77,0x2e,0x64,0x65,0x64,0x65,0x63,0x6d,0x73,0x2e,0x63,0x6f,0x6d,0x20,0x74,0x61,0x72, 0x67,0x65,0x74,0x3d,0x27,0x5f,0x62,0x6c,0x61,0x6e,0x6b,0x27,0x3e,0x50,0x6f,0x77,0x65,0x72,0x20, 0x62,0x79,0x20,0x44,0x65,0x64,0x65,0x43,0x6d,0x73,0x3c,0x2f,0x61,0x3e);
安详配置六:操作伪静态成果克制以下目次运行php剧本
